What is consent.exe?
Consent.exe is a part of the Microsoft Windows operating system which is a secure and legal file and in particular the user account control.
This executable is linked to the installation of Windows 10, Windows Vista UAC developers, and other operations.
So you shouldn’t care about this file if you haven’t found any strange activity on your Mac.
It is launched once the system boots up and typically this file is located in the C folder which has Windows 32 system.
Consent.exe may also be a source of slowdowns on the device and heavy CPU usage. Infect users note different problems and failures caused by this file.
This is likely as the files have increased device rights and remain in the protected place which has made malicious actors become more effective in disguising their processes behind such as common file names.
[box title=”” border_width=”2″ border_color=”#ffb200″ border_style=”solid” bg_color=”#fffbef” align=”left”]If your windows have any sort of error, try using reimage repair. If you want to know in-depth about it, then check out our review of Reimage Repair.
How to Remove It?
Malware developers tend to use the names of the official files to keep the viruses from being deleted.
The background of malicious processes enables heavy usage of Desktop resources and due to the general name and form of the user and file, it stays cool.
Be mindful however that the name consent.exe may often be used to mark the existence of a virus particularly as it tends to run all the time.
[box title=”” border_width=”1″ border_color=”#343e47″ border_style=”solid” bg_color=”#effaff” align=”left”]Deletion of consent.exe is not suggested therefore and this file forms a vital aspect of the operating system.
Thus deleting it or might end up with the numerous code related issues when a malicious application uses this file.
If you think you might have received a computer virus so you can test the position of this file.
Search the computer with a modified antispyware program to ensure it’s not a threat if the file is not in the C folder Windows or Windows 32 system.
We recommend using Reimage to check system files that have to fix those changes in system folders or registry systems.
You may also use some other device that will handle the treatment and removal of consent.exe if appropriate.
If you are a hundred percent malicious to this paper so do not try to remove it on your own. Software viruses are composed of several separate files and are responsible for particular activities.
Therefore you need to delete consent.exe with other harmful files in order to clean up your computer. Malware removal tools are extremely helpful in this case.
[/box]In the executable file, format Malware comes and may be used to produce cryptocurrencies and Mount other malware as a secondary payload at a cost of your PC resources.
These files contain project worms and even harmful scripts that destroy computers and if you think consent.exe virus is on the desktop run a computer device test with the secure anti-malware application.
File Information of consent.exe:
Since the true consent.exe method is an essential part of certain versions of Windows, careful review of the file is needed.
We claim to sense a number of malicious applications occurred that are used to mass themselves as administrative permissions procedures.
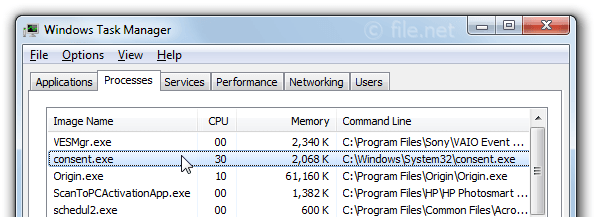
They do so the surveillance scanner will not find it. Let’s access if you are living with an active Malware consent by checking its place of residence then you have to open the task manager by pressing the Control + shift + escape.
And after that, you have to click on the right side of your menu bar for consent.exe and picked to open file location to do so.
If the position is discovered in the C folder for Windows 32 system you can assume the operation is valid.
However, if you want your PC to be extra services so you have to click on the right it is screened on the executable file and picks assets.
Open the visual signatures tab within the properties panel and see whether the signer name is identified as Microsoft Windows.
If Microsoft personally signatures days you have also decided that the file is also legal.
When you have found that the consent.exe mechanism originates from a separate place you are potentially dealing with the virus that hides as a real operation of the program.
We strongly recommend running a powerful protection check on your computer in this situation and we also suggest using Malwarebytes if you don’t have a protection suite ready for this.
The consent.exe method is only named when the user account control is turned on as already stated.
Without this method starting up with the access administrator level to files and configurations which is difficult with every non-windows system.
Having that in mind we may assume that the real consent.exe file is a crucial component of Windows Vista which cannot be removed because the file becomes a virus.
The consent.exe mechanism is considered by technology analysts as one of the only useful protection mechanisms that effectively avoid unintended Malware execution.
[box title=”” border_width=”1″ border_color=”#343e47″ border_style=”solid” bg_color=”#effaff” align=”left”]High CPU Usage of consent.exe:
Consent.exe will sometimes cause high CPU usage and delete the output of the machine and this is likely since the software is in a protected place and has improved device right.
Many people ask the question that may I uninstall the consent.exe?
Okay, removing the constant.exe method isn’t suggested and nevertheless, if it continuously freezes your Mac you may attempt to remove the account user control for a temporary time so the consent does not load until it has shut off UAC.
In the first step, you have to search for the Windows box UAC and after that, you have to click on the change user account control panel settings.
In the second step, the file should be open on Windows then you have to move the slider to the option never notify and click the enter button.
Nonetheless, having the disabled UAC isn’t advised, after resolving your question you will take the above measures to Enter user account control settings and switch back the slider to what it was before.
Do not slip through your own presumption that the consent virus is the malicious software that causes device problems or other computer slowness.
Aside from the ransomware infections, there are lots of different problems that could be the cause of shifts in pace.
Use an anti Malware program or troubleshoot to figure out the explanation behind the annoyance before doing away with it.
[/box]Best Practices for Resolving Consent Issues:
There are instances when the executable consent gets infected and stops downloading or installing your operating system or any non-Windows program on your device.
If you have the same problem so we have been able to find a few possible solutions that have supported people in specific circumstances.
The first method temporarily disabled the control of the user’s account. If it didn’t work to restart the catalog database you can bypass functionality of Consent.exe by disabling temporarily user account control.
It will encourage you to update or install or uninstall any previously failed non-Windows applications which only note to re-enable the user account control until deployment is complete.
So here is a simple guide to disable the user account control which is available here.
Method #1:
In the first step, you have to open the start bar for windows in the bottom left corner and check for user account control after that you have to click on settings to alter the user account settings.
In the second step, there is a setting user account control window by which you can slide down the tone to never notify and hit the enter button.
In the third step with a user account control which is disabled or performs the previously failing software installation or uninstallation.
So you have to switch to the account control setting Window through Phase one once the configuration is full and adjust the slider to what it was before.
Bear in mind that the root problem will persist, even though you manage to update the non-Windows programs by disabling user account control.
Most possibly the device suffers from a compromised consent.exe script. By encouraging a device to install the new upgrades and hotfixes you will seek to solve the problem.
If it fails you have to try reset your Windows by visiting how to reset Windows.
Also Read: What is cnsemain.exe? How to Remove it?
Method #2:
In the second method, you have to fix software collection with essential.
By using an elevated command prompt to repair the catalog database using the command Esentutl some users have managed to solve the problem by this method.
But note that it is only possible if you boot your machine in secure mode and here is a quick through the entire thing.
In the first step, you have to use the start bar for Windows and press the power button and keep downshift before pressing restart and in safe mode, this will reset the device.
In the second step after booting into safe mode restart the windows bar which is at the bottom left corner on your screen and check for command.
After that, you have to click on the right prompt order and pick it up as an administrator.
By typing net stop Cryptsvc, in the elevated command prompt and after that you have to hit enter and to encourage the next step this should interrupt the cryptographic services.
In the fourth step, you have to type essential and check the percentage root in the Windows 32 system and hit the enter button.
If you will see the error in the denied access so you will not be booted into safe mode.
In the fifth step, you have to select ok if ask a Fame you will only work on compromise databases, and in the last step.
You have to click on net start cryptographic services after the procedure is complete and press enter to restart the cryptographic services.
[box title=” ” border_width=”2″ border_color=”#fff8e5″ border_style=”solid” bg_color=”#fff8e5″ align=”left”]Click Here to Run a free Scan for consent.exe Related Errors.